zynamics BinNavi is the leading open source binary code reverse engineering tool
based on graph visualization
Description
BinNavi is a binary code reverse engineering tool that was built to assist vulnerability researchers who look for vulnerabilities in disassembled code.
With BinNavi you can analyze disassembled x86, ARM, PowerPC, and MIPS code using the powerful built-in static code analysis techniques. In cases where static code analysis is not enough, you can use the built-in debuggers to get a live view on the program you are analyzing.
The code is available on GitHub.
Note: This product is no longer under active development.
BinNavi is a binary code reverse engineering tool that was built to assist vulnerability researchers who look for vulnerabilities in disassembled code.
With BinNavi you can analyze disassembled x86, ARM, PowerPC, and MIPS code using the powerful built-in static code analysis techniques. In cases where static code analysis is not enough, you can use the built-in debuggers to get a live view on the program you are analyzing.
The code is available on GitHub.
Note: This product is no longer under active development.
Use Cases
To learn more about the features and use cases of BinNavi please take a look at the BinNavi manual.
- Do control flow based code analysis of disassembled x86, ARM, MIPS, and PowerPC code
- Cut down on complexity by removing unimportant code from functions
- Use powerful remote debuggers to debug programs on different operating systems
- Use Differential Debugging to quickly locate relevant code
- Create and assign user-defined tags to mark important functions and basic blocks
- Use advanced code analysis algorithms to keep track of data and code
- Manage all your reverse engineering projects in one central database
- Write scripts and plugins to extend BinNavi to meet your specific goals
- Rename and annotate variables and functions to make them self-explanatory
- Use the REIL meta-language to write platform-independent program analysis code
To learn more about the features and use cases of BinNavi please take a look at the BinNavi manual.
Screenshots
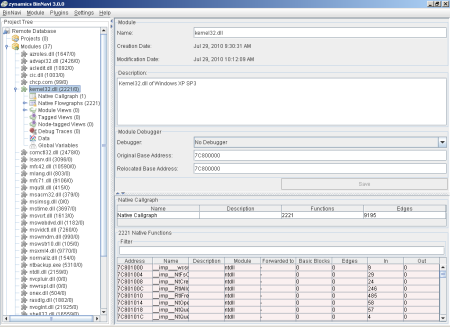
Screenshot 1: BinNavi 3.0 main window
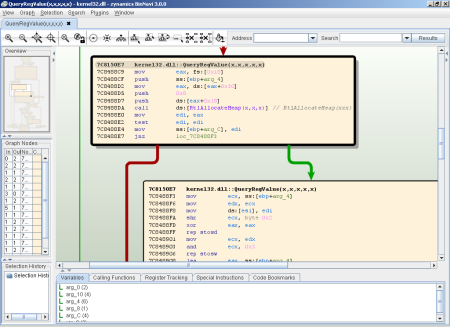
Screenshot 2: BinNavi graph window
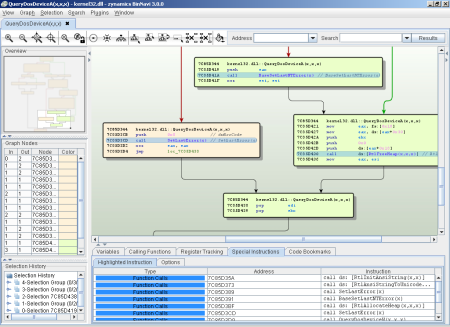
Screenshot 3: Highlighting call instructions in disassembled code
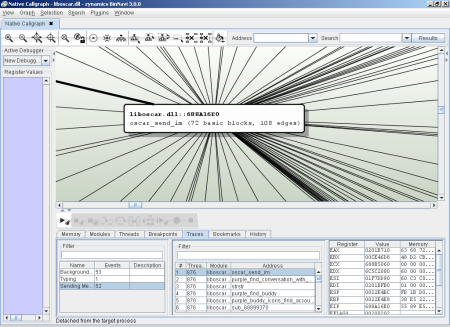
Screenshot 4: Debug trace that logs registers and memory values
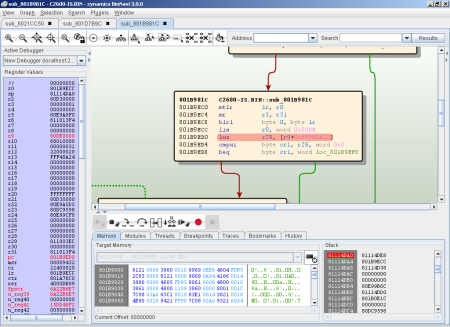
Screenshot 5: Debugging a Cisco 2600 router (Using GDB Agent, see below)
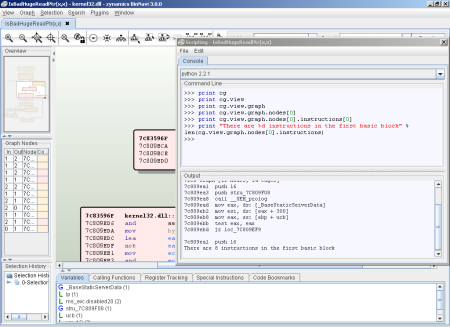
Screenshot 6: Using scripts to access disassembly data
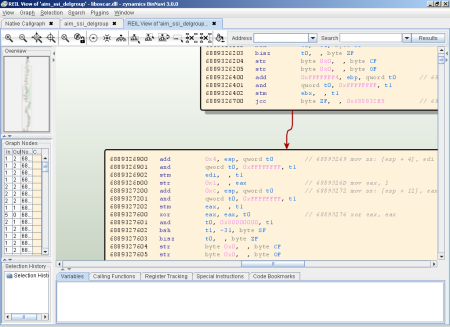
Screenshot 7: Using the platform-independent intermediate language REIL